Security

AI-Powered Code Editors Could Have Become Malware Delivery Machines: Here's What Happened
- Turker Senturk
- Security
- 7 min read
- 06 Jan, 2026
If you're a developer using AI-powered code editors like Cursor, Windsurf, or Google Antigravity, you might want to pay attention to this one. Security researchers have uncovered a vulnerability that
read more
VVS Stealer: How This Python-Based Malware Targets Discord Users Through Advanced Obfuscation
- Turker Senturk
- Security , Technology
- 10 min read
- 06 Jan, 2026
If you're a Discord user, you might want to pay attention to this one. Security researchers have recently uncovered a nasty piece of malware called VVS Stealer (sometimes written as VVS $tealer) that'
read more
Docker Hardened Images: Making Container Security Free and Accessible for Everyone
- Turker Senturk
- Technology , Security
- 5 min read
- 18 Dec, 2025
Introduction Docker has just announced a watershed moment for the container ecosystem: Docker Hardened Images (DHI) are now free and open-source for everyone. This groundbreaking move transforms how d
read more
Docker Desktop 4.50: Revolutionizing Development Workflows
- Turker Senturk
- Software , Security
- 2 min read
- 29 Nov, 2025
Key HighlightsFaster debugging workflows with Docker Debug now free for all users Enhanced security controls with granular control over container behavior and seamless enterprise policy integrations S
read more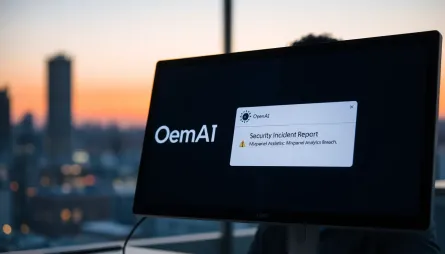
OpenAI Addresses Mixpanel Security Incident
- Turker Senturk
- AI , Security
- 2 min read
- 27 Nov, 2025
Key HighlightsA security incident occurred at Mixpanel, affecting limited analytics data related to some OpenAI API users No sensitive information, such as passwords, API keys, or payment details, was
read more
Revolutionizing AI-Driven Development with Snyk Studio for Qodo
- Turker Senturk
- AI , Security
- 2 min read
- 24 Nov, 2025
Key HighlightsSnyk Studio for Qodo embeds security intelligence into AI development workflows Automated detection and fixing of security vulnerabilities in real-time Qodo's Agentic Code Quality Platfo
read more
AI-Orchestrated Cyber Espionage: A New Threat
- Turker Senturk
- AI , Security
- 3 min read
- 17 Nov, 2025
Key HighlightsThe first reported AI-orchestrated cyber espionage campaign was detected in mid-September 2025. The campaign, attributed to a Chinese state-sponsored group, used AI models to execute att
read more
Chrome Update: 20 Security Fixes Released
- Turker Senturk
- Security
- 2 min read
- 04 Nov, 2025
As the world's most widely used browser, with an estimated 3.4 billion users, Chrome's security is a top priority. This move reflects broader industry trends, where tech giants are investing heavily i
read more
VPN Technology in 2025: A Comprehensive Guide to Protocols, Security, and Provider Comparison
- Turker Senturk
- Technology , Security
- 14 min read
- 03 Nov, 2025
By 2025, Virtual Private Network (VPN) technology has evolved from a niche cybersecurity tool into a mainstream infrastructure component trusted by approximately one-third of global internet users. Th
read more
ChatGPT's Enhanced Safety Features for Sensitive Conversations
- Turker Senturk
- Security
- 2 min read
- 27 Oct, 2025
As the use of AI chatbots like ChatGPT becomes increasingly prevalent, ensuring user safety and well-being is of paramount importance. This move reflects broader industry trends towards prioritizing A
read more
OpenAI Enhances GPT-5 Safety
- Turker Senturk
- Security
- 2 min read
- 27 Oct, 2025
As the use of AI models like GPT-5 becomes increasingly widespread, the need for these models to handle sensitive conversations with care and empathy has never been more pressing. This move reflects b
read more
MCP Prompt Hijacking: A New AI Security Threat
- Turker Senturk
- AI , Security
- 2 min read
- 24 Oct, 2025
As artificial intelligence (AI) becomes increasingly integral to business operations, a new security threat has emerged, targeting the protocols that enable AI systems to interact with each other and
read more
Unlocking Secure AI Workloads with Confidential VMs
- Turker Senturk
- Software , Hardware , Security
- 3 min read
- 21 Oct, 2025
As the AI landscape continues to evolve, the need for secure and confidential computing has become a top priority. This move reflects broader industry trends towards prioritizing data protection and s
read more
Unity Uncovers Decade-Old Security Flaw Affecting Game Developers Worldwide
- Turker Senturk
- Security , Technology
- 2 min read
- 06 Oct, 2025
Unity Technologies has issued an urgent warning to developers after discovering a critical security vulnerability that has existed undetected in its game engine for almost a decade. The flaw, affectin
read more